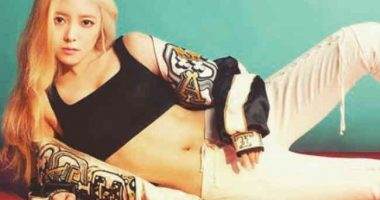
Lee Se-young Diet Plan and Workout Routine
Lee Se-young Diet Plan and Workout Routine: Lee Se-young is an actress and model known for her roles in movies and TV shows like The Red Sleeve, The Crowned Clown, Doctor John, A Korean Odyssey, When I Turned Nine, Hot Young Bloods, etc. She is also well known for her beautiful body shape and slender… Read More »